Importance of security audits
In today’s interconnected world, where data centers serve as the guardians of valuable information, the significance of comprehensive security audits cannot be overstated. Recent incidents have shed light on the critical need for subject matter experts to conduct audits, ensuring the implementation and verification of industry best practices.
Best Practices
At Willowmore, we understand the gravity of data center security, and we collaborate closely with our partners to establish and uphold the following best practices:
✅ Properly Secured Cabinets
We ensure that all cabinets are securely locked, allowing access only to authorized personnel assigned to specific racks. This stringent measure guarantees that only those with the necessary permissions can interact with sensitive equipment.
✅ Controlled Access Time Windows
Contractors are provided with clearly approved time windows to access servers within data centers. This structured approach ensures that their activities align with the overall security protocols and limits potential risks.
✅ Identity Verification of Contractors
Identity checks are meticulously conducted on all contractors present on-site. By confirming their identities, we maintain a heightened level of accountability and diminish the likelihood of unauthorized access.
✅ Digital Audit Trail
To establish a robust accountability framework, we maintain a comprehensive digital audit trail. This trail records every instance of access, including who accessed the site, the reason for access, the timing of the entry, and whether the equipment was properly secured upon exit. This record-keeping provides transparency and enables swift response in case of any security incidents.
Our Solution
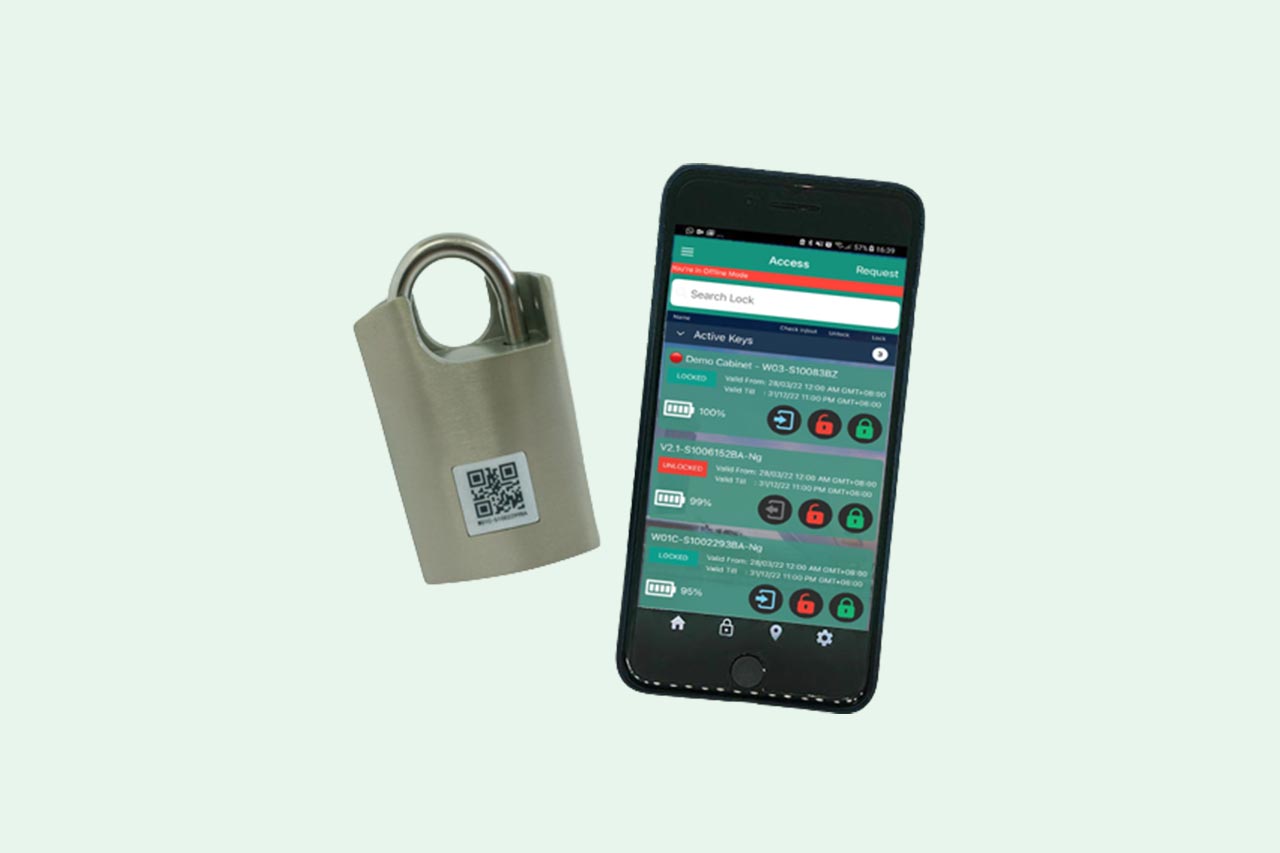
Our solution is designed to ensure that our customers can quickly install new cabinets or retrofit existing cabinets to enable digital smart locks.
The best part? This process eliminates the need for cumbersome additional cabling and provisioning of IP addresses, making the operations both secure and user-friendly.
SECURE and Easy Authentication
To ensure the utmost protection, our solution offers multiple authentication methods. Identities can be authenticated using secure passwords or advanced biometric measures, adding an extra layer of security to safeguard sensitive data.
By implementing these comprehensive security measures and utilizing our innovative solution, we empower our customers to enhance physical security at their data centers effectively. Together, let’s stay one step ahead in safeguarding our valuable digital assets!